Email and tracking techniques
"Recommendation"
"Confidential Approach"
"Keen to speak"
🙄
Cold emails (sending an unsolicited email for business purposes) are an unfortunate fact of life. Tenacious reps exhibit an admirable amount of self-drive, but I really dislike tracking techniques common to emails.
Tracking pixels
Invisible to the eye are 1x1 pixel "images" embedded in email messages as an <img> tag:
<img src="https://visit.test.io/api/mailings/opened/PMRGSZBCHI4DQOJWGA4CYITPOJTSEORCME4TGOJSHA4GILLFMVSDCLJUGY4WKLJYHFRTSLJTMMZTSNLBHAZDMMDBG4RCYITWMVZHG2LPNYRDUIRUEIWCE43JM4RDUITDJRSE6WKMPJXFIMTOIJWS2TSWNRIGYULUKJKES3LCIZDE6YLFMJKVAQ3EFVEFSS32NBTT2IT5.gif" alt="" width="1" height="1">
An actual tracking pixel from a recent email, which you can view yourself.
When you open the email, your email client usually renders the HTML, which involves making an HTTP request for the image resource. Embedded in the URL is a token which is tied on the sender's side to the email having been sent to me. So they can just check the web server's logs to see if this image has been accessed, and if so, they can assume I've read opened the email.
Some email clients allow you to not download images automatically, preventing tracking pixels from being downloaded and performing their job. Thunderbird is a good example of an extremely security conscious email client.
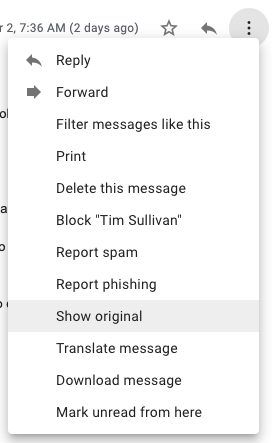
In Gmail's web client, you can Show Original which opens the email source code in a new tab, from there you can search for an <img> tag. Some email sources come base64 encoded, which you can decode online or in the terminal.
Tracking links
Utilizing the same token idea, links can contain identifying information in the form of HTTP paths or parameters to identify if you've clicked on a link or not.
<a href="https://tracking.mindfireinc.com/?ref=-CsAADuh-pASrVfpUwIrE5P7dE0XHpEmAQAAAIVenf2k39WP84fUdXAVs42qQHYZphXa1FaVaNqm7rGMz90ZFlpFK1BhIVA1TK6Se951uxTx5ZYEB4nHc6Jn4LqOvZBwK27cYCvfnpu0gO0Opj2Rfjc1KArXqmC-UmWpef6gV7z-czR20DiMwhmP51e__U8yWp-w4gSbklCc2SdnVZZGN0_BC5OXcWPD8OtMV_grL8K95IrisH2x-0CfA2pAMvpNpuvle03TUNfMb0GStqIgWB8__7VUOaaHBZaa62I1vhGuYxe-tut9D6Z-VTqurMocFRTZiRb_jQkvbM1F8CeeH_ZMjb0Z9-IHNvG1Cw">Click here!</a>
An actual tracking link from a recent email.
This example uses an HTTP parameter, ref, which the web server will be able to log and indicate I have visited the link.
Preventing tracking pixels and links
The bad news: Tracking links have the potential to be required in order to obtain a resource. The remote administrator could enforce a tracking token be present in the HTTP request before returning the resource. (I will think if there are other ways to side-step tracking links.)
More bad news: There are browser extensions to specifically block tracking pixels. While more of an art than a science, the main concern here is that the extension must have access to your email content. This then means that you must trust the extension developer since they could selectively submit your email data to a remote system.
The good news: As mentioned, email clients provide settings to download images or not, allowing you to view emails without grabbing images, albeit potentially malformed due to the said lack of images.
Some other thoughts to combat tracking pixels:
- A ubiquitous email client could choose to make an HTTP request for all resources, but immediately abort the HTTP request. This would show that all resources are fetched, without spending the cost of downloading all bytes. This makes it seem as if all persons do view an email with trackers. The benefit here lies in numbers -- if "everyone" is tracked, no one is.